 MapYourTech | Optical Security
MapYourTech | Optical Security
Quantum-Safe Optical Networks: Encryption, QKD, and Long-Term Security Planning
Analysis of Layer-1 optical encryption, Quantum Key Distribution protocols and deployment challenges, NIST post-quantum cryptography standards, and how the ITU-T ION-2030 framework addresses quantum resilience in next-generation optical infrastructure.
1. Introduction
Optical transport networks carry the majority of the world's long-haul and metropolitan data traffic. Financial settlements, government communications, healthcare records, and real-time control signals for critical infrastructure all traverse these fiber systems. For decades, the dominant model treated the physical layer as intrinsically secure: light guided inside a glass strand in a locked conduit seemed difficult to tap without detection. That assumption no longer holds unconditionally, and a new class of threat is amplifying the concern.
The emergence of large-scale quantum computers creates a future scenario in which today's encrypted traffic, even if unreadable today, could be decrypted tomorrow. Attackers operating under the so-called harvest now, decrypt later (HNDL) strategy are already capturing and archiving encrypted optical traffic. When cryptographically relevant quantum computers become available, the archived ciphertext becomes accessible. For data with a secrecy horizon measured in decades — classified government communications, long-term financial instruments, medical records — the threat is not hypothetical: it is present and active today.
The optical networking community has responded along two parallel tracks. The first track applies quantum mechanics directly to the security problem through Quantum Key Distribution (QKD), generating encryption keys whose secrecy is guaranteed by physical law rather than computational hardness. The second track develops Post-Quantum Cryptography (PQC), which replaces mathematically vulnerable algorithms with new ones believed to resist both classical and quantum attack. Both approaches have reached a practical threshold: QKD deployments now span metro and even long-haul segments, while the US National Institute of Standards and Technology (NIST) finalized its first PQC standards in August 2024.
The ITU-T Study Group 15 framework ION-2030 — International Optical Networks towards 2030 and Beyond — explicitly identifies quantum-resilient design as one of its four principal advances alongside terabit-per-second connectivity, AI-native intelligence, and energy efficiency. This article examines the full security landscape: encryption at Layer 1, QKD physics and deployment experience, the NIST PQC standards, hybrid architectures that combine both approaches, and how network operators should plan migration over the coming decade.
2. The Quantum Threat to Optical Networks
2.1 Why Classical Cryptography Is at Risk
The two most widely deployed public-key cryptography families are RSA and elliptic-curve cryptography (ECC). Both derive their security from mathematical problems that are computationally intractable on classical computers: integer factorisation for RSA, and the discrete logarithm problem for ECC. In 1994, Peter Shor demonstrated that a sufficiently large quantum computer running Shor's algorithm could solve both problems in polynomial time, rendering key lengths that are secure today completely breakable tomorrow.
Shor's algorithm requires a fault-tolerant quantum computer with millions of high-quality logical qubits. Physical implementations as of 2026 are far from this threshold, but the engineering trajectory suggests that cryptographically relevant machines could emerge within the coming decade — with some expert estimates placing this between 2030 and 2035. The NIST post-quantum cryptography project, launched in 2016, cited this same 2030 horizon as justification for urgency.
Nation-state actors and sophisticated threat groups do not need a quantum computer today to benefit from one tomorrow. By capturing and archiving encrypted optical traffic now, they can decrypt it once a capable quantum machine becomes available. Any data transported over optical networks today that must remain confidential beyond approximately 2030 is already at risk if protected only by RSA or ECC. Long-haul submarine cables and inter-data-centre links carrying financial and government data are primary targets.
Symmetric key algorithms such as AES are also affected, but less severely. Grover's algorithm provides a quadratic speedup against symmetric ciphers, effectively halving the key security level. AES-128 reduces to approximately 64 bits of security against a quantum adversary; AES-256 reduces to approximately 128 bits, which remains acceptable by current standards. For this reason, symmetric encryption at AES-256 is often considered "quantum-safe" at its current key length, provided the key exchange mechanism itself is also quantum-safe.
2.2 The Optical Layer Threat Surface
The threat surface for optical networks extends beyond key exchange. At the physical layer, optical tapping through fiber bending or splitter insertion can extract a fraction of guided light without interrupting service. The signal-to-noise ratio of a tapped signal may be poor, but for passive wavelength-division multiplexed (WDM) signals carrying unencrypted data, even partial interception is meaningful. Layer-1 encryption addresses this directly by encrypting the data stream before it enters the optical amplification and multiplexing chain.
At the management and control plane, network elements communicate configuration data and topology information that, if compromised, enables traffic diversion and man-in-the-middle attacks. Post-quantum cryptography protects these control channels, as they typically use TLS, SSH, or IPsec — all of which rely on RSA or ECC for key establishment.
3. Layer-1 Optical Encryption Principles
3.1 What Layer-1 Encryption Covers
Layer-1 (L1) encryption refers to encrypting the data payload at the optical transport layer before framing, multiplexing, or amplification. Unlike Layer-2 Media Access Control security (MACsec, IEEE 802.1AE) or Layer-3 IPsec, which operate on packets or frames, L1 encryption operates on the entire bitstream — including both payload and overhead. This delivers two advantages: it eliminates the protocol overhead cost of higher-layer encryption on dense, short-packet traffic, and it protects the stream at the lowest possible point in the network, before any traffic-handling node can see the plaintext.
MACsec at Layer 2 is widely deployed and interoperable across multi-vendor environments. Its overhead, however, can exceed 20% of link capacity on highly utilised links with predominantly short packets. L1 encryption implemented within coherent DSP ASICs adds negligible overhead and operates at full line rate, but applies only to the WDM segment between two endpoints. Multi-layer environments typically need both: L1 for the transport span and MACsec or IPsec for end-to-end service assurance.
3.2 Technical Implementation in Coherent Systems
In modern coherent optical transceivers, the Digital Signal Processor (DSP) ASIC handles chromatic dispersion compensation, polarisation-mode dispersion compensation, modulation and demodulation, and forward error correction (FEC). The same ASIC architecture is well-suited to incorporate an AES-256-GCM encryption engine with minimal additional silicon area. Encryption and decryption operate in the electrical domain before and after the optical-electrical conversion, respectively, at full line rate.
Key management for L1 encryption requires a secure key exchange mechanism that operates independently of the encrypted data channel. In practice, keys are distributed via a separate out-of-band or in-band management channel, with key rotation managed by a key management server. Key rotation intervals are configurable; common practice is to rotate session keys every 24 hours or upon each new connection, while maintaining continuous traffic flow by overlapping key epochs.
3.3 Performance Characteristics
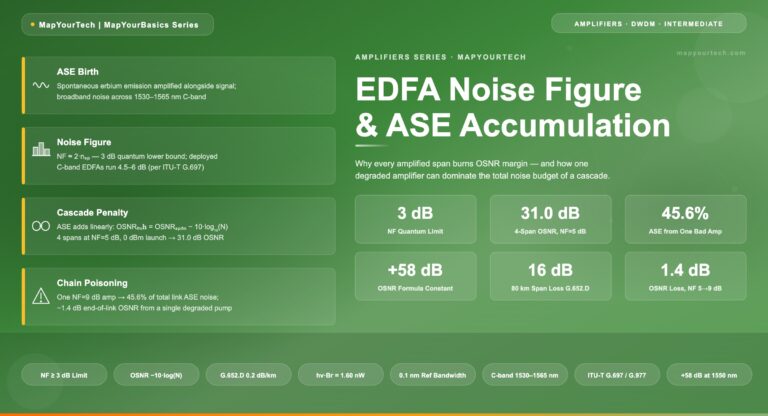
L1 encryption in coherent DSPs designed at advanced process nodes adds typically less than 1 microsecond of latency, which is negligible compared to propagation delay on spans of any practical length. Power consumption overhead is small at these process nodes; the impact is governed primarily by AES-GCM engine clock frequency and memory bandwidth rather than logic area. Importantly, L1 encryption does not affect optical performance metrics such as Optical Signal-to-Noise Ratio (OSNR), chromatic dispersion tolerance, or bit error rate — the encryption and decryption are electrical operations that are transparent to the photonic layer.
/* Ciphertext and authentication tag generation */
C = AES-CTR(K, IV, P)
T = GHASH(H, A, C)
Where:
K = 256-bit symmetric key
IV = 96-bit initialisation vector (unique per key)
P = Plaintext payload
C = Ciphertext output
H = Hash subkey = AES(K, 0128)
A = Additional Authenticated Data (AAD)
T = 128-bit authentication tag (integrity & authenticity)
Security level vs. Grover's algorithm:
AES-256 → ~128-bit quantum security (Grover halves effective key length)4. Quantum Key Distribution: Protocols and Physics
4.1 Foundational Principles
Quantum Key Distribution (QKD) is a family of protocols that generate a shared random key between two parties — conventionally named Alice and Bob — with security guaranteed by the laws of quantum mechanics rather than by computational assumptions. The core insight follows from the no-cloning theorem: an unknown quantum state cannot be copied without disturbing it. Any eavesdropper (Eve) attempting to intercept quantum-encoded key bits inevitably introduces detectable errors. Alice and Bob can therefore bound the maximum information Eve may have obtained and, if that bound is acceptable, perform privacy amplification to distil a provably secure key.
All QKD protocols require two channels: a quantum channel for transmitting quantum states, and a classical authenticated channel for reconciliation and privacy amplification. Eve is assumed to have full control over the quantum channel, unlimited classical computation, and access to any technology permitted by physics — except she cannot access Alice's and Bob's apparatus, and she cannot intercept the classical channel without detection (authentication is required).
The security of QKD rests on the quantum bit error rate (QBER). When Eve intercepts and re-transmits quantum states, the QBER increases from its baseline (equipment noise floor) by an amount that depends on her strategy and the protocol. If the measured QBER exceeds a protocol-specific threshold, Alice and Bob abort the session. If it is below the threshold, they perform error correction and privacy amplification to generate a secure final key whose length is reduced in proportion to the estimated information leaked to Eve.
4.2 Key Protocols
BB84 Protocol
The original and most widely deployed QKD protocol, proposed by Bennett and Brassard in 1984. Alice encodes key bits in the polarisation of single photons using two conjugate bases. Bob measures in a randomly chosen basis; they keep only the results where bases matched (sifting). Practical implementations use attenuated laser pulses with decoy-state techniques to resist photon-number-splitting attacks. Proven secure against coherent attacks in the asymptotic regime.
E91 / Entanglement-Based
Proposed by Ekert in 1991, using entangled photon pairs. Security is verified through violation of Bell inequalities rather than bit error rate alone. Provides device-independent QKD (DI-QKD) in principle, though practical DI-QKD over useful distances remains a research challenge due to detection efficiency requirements. Used in satellite-based demonstrations.
Continuous Variable QKD
Encodes key information in the continuous quadrature amplitudes (amplitude and phase) of coherent or squeezed light states, measured with homodyne or heterodyne detection. CV-QKD is compatible with standard coherent optical transceivers and uses conventional photodetectors rather than single-photon detectors, simplifying integration into existing telecom infrastructure. The first CV-QKD network was demonstrated in Shanghai.
MDI-QKD
Measurement-Device-Independent QKD removes all detector-side vulnerabilities by having both Alice and Bob send photons to an untrusted central relay (Charlie) that performs a Bell-state measurement. No information about the key is leaked through Charlie even if he is fully compromised. This architecture suits metro networks where the central office is managed by a third party.
4.3 One-Time Pad Integration
The information-theoretic security of QKD is fully realised when the generated keys are used with a one-time pad (OTP) cipher. In OTP encryption, each bit of plaintext is XOR'd with a corresponding bit of a truly random, never-reused key string. The result is provably unbreakable regardless of the adversary's computational power. The practical bottleneck is key rate: OTP requires a key bit for every plaintext bit, so a 100 Gbps OTP-encrypted channel needs a QKD key generation rate of 100 Gbps. No current QKD system approaches this, making OTP-over-QKD suitable only for low-bandwidth, extremely sensitive channels. In practice, QKD-generated keys are used to periodically refresh symmetric cipher keys (typically AES-256), striking a balance between quantum-guaranteed key exchange and high-throughput encryption.
Figure 1: QKD-secured optical link architecture showing the quantum channel, classical authenticated channel, data channel, and key management server interactions.
5. QKD Deployment Realities and Challenges
5.1 Milestones in Fiber-Based QKD
The world's first bank transfer using fiber-based QKD took place in Vienna in 2004. In 2007, ID Quantique transmitted Swiss election results over a 100 km optical fiber link using QKD. The 2008 EU-funded SECOQC project connected six nodes across Vienna and St. Poelten using 200 km of fiber, demonstrating multiple QKD protocol variants simultaneously. In 2010, the Tokyo QKD Network, an international collaboration involving Japanese operators, Toshiba Research (UK), and ID Quantique (Switzerland), demonstrated encrypted video communications at distances up to 45 km with an average secure key rate of approximately 293 kbps.
China has invested heavily in QKD infrastructure. The Beijing–Shanghai quantum backbone, spanning approximately 2,000 km with 32 trusted relay nodes, has been used for government and banking communications. The QUESS satellite mission established quantum-secured key exchange between ground stations separated by over 1,200 km via satellite relay, demonstrating that the photon loss model for satellite links — which scales quadratically with distance rather than exponentially as in fiber — offers a path to global QKD without quantum repeaters.
5.2 Key Rate vs. Distance
The secure key generation rate in fiber-based QKD falls sharply with distance because channel loss reduces the number of usable photon events per second. At 10 km of standard single-mode fiber, modern commercial DV-QKD systems typically achieve secure key rates in the range of tens to hundreds of kbps. At 100 km, this drops to single-digit kbps or lower. Beyond approximately 150 km, the secure key rate in direct fiber-based systems approaches zero without quantum repeaters.
Trusted relay nodes extend the reach by having each segment exchange keys independently, with an operator-trusted node at each relay location. The practical implication is that the end-to-end security model depends on the trustworthiness of each relay node — a significant constraint for cross-border or multi-operator deployments. Twin-field QKD (TF-QKD), a protocol variant where interference of photons at a central point allows key generation across longer distances, has demonstrated key exchange at distances exceeding 500 km in laboratory settings, pointing toward future field deployments without trusted relays at intermediate distances.
Figure 2: Approximate secure key rate vs. fiber distance for representative QKD approaches. Values are indicative of published experimental and commercial system performance; actual rates depend on protocol, detector technology, and fiber loss coefficient.
5.3 Integration with DWDM Networks
A significant practical challenge is co-propagating quantum signals alongside conventional DWDM channels on the same fiber. The single-photon-level quantum signals are extremely sensitive to noise photons generated by Raman scattering from the intense classical channels. Several strategies address this: using the quantum signal in the O-band (around 1310 nm) while classical traffic uses the C-band (1530–1565 nm), or placing the quantum channel at a wavelength separated by at least 25–50 nm from the nearest DWDM channel and applying narrow bandpass filtering at the receiver. Some operators dedicate a separate dark fiber for the quantum channel entirely, avoiding co-propagation noise at the cost of requiring additional fiber infrastructure.
CV-QKD offers a potential advantage here: coherent detection is inherently narrowband and the signal characteristics are closer to standard telecom signals, making co-propagation with classical DWDM channels more tractable than for discrete-variable single-photon approaches. Several CV-QKD demonstrations have used standard coherent receiver hardware to simultaneously receive classical data and perform QKD measurements on the same transceiver with wavelength separation.
5.4 Side-Channel Attacks and Device Security
QKD security proofs assume ideal devices. Real implementations have imperfections that create side-channel vulnerabilities. The detector-blinding attack, demonstrated in 2010, used a continuous bright laser to saturate single-photon detectors into a linear response regime, allowing Eve to control detector outputs without introducing the expected quantum errors. Countermeasures such as random detector efficiency variation were developed but subsequently defeated by refined attacks. This ongoing cycle highlights the gap between security proofs and certified deployed devices.
Measurement-Device-Independent QKD (MDI-QKD) addresses detector-side vulnerabilities by removing all measurement devices from the trusted domain. Twin-field QKD inherits this property while also extending reach. Device-Independent QKD (DI-QKD) extends the principle to all devices, but requires loophole-free Bell inequality violations at high rates — a target that laboratory demonstrations have recently approached but that practical deployment still requires significant distance to achieve.
Section Summary — QKD Deployment
- Fiber QKD mature at metro distances; secure key rates drop sharply beyond 100 km without trusted relays.
- Satellite QKD enables inter-continental key exchange; China's QUESS mission demonstrated >1,200 km entanglement.
- Co-propagation with DWDM requires careful wavelength management; CV-QKD offers better telecom integration.
- Real devices have implementation vulnerabilities; MDI-QKD and TF-QKD architectures mitigate detector attacks.
- Quantum repeaters remain a research milestone required for global all-fiber QKD networks without trusted relays.
6. Post-Quantum Cryptography: NIST Standards
6.1 The NIST Standardisation Programme
Post-Quantum Cryptography (PQC) refers to classical algorithms — those running on conventional computers — that are designed to resist attack by both classical and quantum computers. Unlike QKD, PQC does not require new hardware infrastructure; it replaces the mathematical problem underlying key exchange and digital signatures with one that is believed to be hard for quantum computers.
NIST launched its PQC standardisation competition in 2016, receiving 82 submissions. After multiple rounds of public evaluation and cryptanalysis, NIST published the first three finalised PQC standards on August 13–14, 2024, which became effective under Federal Information Processing Standards. On March 11, 2025, NIST announced the selection of HQC as a fifth algorithm for key encapsulation, serving as an alternative to ML-KEM with a different mathematical foundation as a backup.
| Standard | Algorithm | Type | Mathematical Basis | Security Categories | Use Case |
|---|---|---|---|---|---|
| FIPS 203 | ML-KEM | Key Encapsulation Mechanism (KEM) | Module Learning with Errors (MLWE) | 1, 3, 5 (512, 768, 1024) | General encryption, TLS key exchange, VPN |
| FIPS 204 | ML-DSA | Digital Signature | Module Learning with Errors (MLWE) — lattice | 2, 3, 5 (44, 65, 87) | Code signing, certificate authentication |
| FIPS 205 | SLH-DSA | Digital Signature | Hash-based (SPHINCS+ family) | 1–5 (12 parameter sets) | Long-term archival, conservative security |
| Draft FIPS 206 | FN-DSA (FALCON) | Digital Signature | NTRU lattice (FFT-based) | 1, 5 | Compact signatures, high-throughput auth |
| In progress | HQC | Key Encapsulation Mechanism | Code-based (quasi-cyclic codes) | TBD | ML-KEM backup; different math foundation |
6.2 ML-KEM (FIPS 203) — Key Encapsulation for Optical Network Control Planes
ML-KEM is the primary standard for establishing shared secrets over a public channel and is the direct replacement for RSA and ECC-based key exchange in protocols such as TLS, SSH, and IPsec. It is a Key Encapsulation Mechanism (KEM): one party generates a public key, the other encapsulates a shared secret against it, and both parties derive the same secret through decapsulation. Security rests on the computational hardness of the Module Learning with Errors (MLWE) problem, which is believed to be intractable for quantum computers.
Three parameter sets are defined: ML-KEM-512 (Category 1, comparable to AES-128), ML-KEM-768 (Category 3, recommended default), and ML-KEM-1024 (Category 5, comparable to AES-256). For optical network management plane applications — NMS–NE communication, YANG/NETCONF sessions, controller-to-controller links — ML-KEM-768 provides an appropriate balance of security and performance. The public key for ML-KEM-768 is 1,184 bytes and the ciphertext 1,088 bytes, both manageably small for management plane protocols.
6.3 ML-DSA (FIPS 204) — Signatures for Network Authentication
ML-DSA replaces ECDSA and RSA signatures in digital certificates, code signing, and protocol authentication. It offers three parameter sets (ML-DSA-44, ML-DSA-65, ML-DSA-87) with a balanced trade-off between signature size, key size, and performance. For optical network operators, the most immediate application is in network element certificates and control plane authentication: BGP-4 route authentication, RSVP-TE signalling integrity, and TLS certificates for element management systems. NIST's transition timeline under NIST IR 8547 plans to deprecate quantum-vulnerable algorithms from federal standards by 2035, with high-risk systems transitioning earlier.
6.4 SLH-DSA (FIPS 205) — Conservative Long-Term Security
SLH-DSA, based on the SPHINCS+ hash-based signature scheme, offers security that depends only on the collision resistance of standard hash functions — a far more conservative assumption than lattice hardness. The trade-off is larger signatures (8 kB to 50 kB depending on parameter set) and slower signing. SLH-DSA is well-suited for long-term archival signatures, firmware update authentication for optical network elements, and any scenario where security must be defensible decades from now regardless of advances in lattice cryptanalysis.
Figure 3: Comparison of public key sizes for classical (RSA-3072, ECDSA P-256) and post-quantum (ML-KEM-768, ML-DSA-65, SLH-DSA-SHA2-128s) algorithms. Larger keys require adjustments in certificate infrastructure and handshake buffer sizes.
7. Hybrid Security Architectures
7.1 QKD + Classical Encryption (Layer-1 Hybrid)
The most practical near-term deployment combines QKD-generated keys with conventional symmetric encryption. QKD is responsible for key generation and distribution; AES-256-GCM handles the actual data encryption at line rate. This hybrid approach means the security of the data channel is protected as long as either QKD or AES-256 remains unbroken. If QKD key exchange is disrupted (equipment failure, physical attack on the quantum channel), the system falls back to a pre-shared AES key. If a quantum computer becomes available, the AES encryption still provides 128-bit equivalent security against Grover's attack even without the QKD component.
7.2 QKD + PQC (Control Plane Hybrid)
QKD secures the key exchange for the data plane; PQC secures the control plane. This pairing addresses the two distinct threat surfaces of an optical network. Network management sessions, GMPLS/OSPF-TE adjacency authentication, NETCONF sessions, and SDN controller links cannot wait for a dedicated quantum channel; they run over TCP/IP and need PQC now. QKD-generated keys, delivered via the key management server, protect the data transport encryption. The combination means an attacker must simultaneously break the QKD channel security (which requires violating quantum mechanics) and the PQC control plane (which requires breaking MLWE hardness), with no single point of failure.
7.3 Hybrid PQC Key Exchange (ML-KEM + ECDH)
During the transition period, hybrid key exchange combines a post-quantum KEM with an existing classical algorithm. For TLS connections, this typically means X25519MLKEM768: an X25519 Diffie-Hellman exchange combined with ML-KEM-768, where the final shared secret is derived from both. If ML-KEM is later found to have an unexpected vulnerability, the X25519 component still provides classical security. If a quantum computer breaks X25519, ML-KEM still protects the session. NIST's guidance permits this hybrid approach under FIPS 140 compliance as long as at least one of the combined algorithms is FIPS-approved. Industry deployment of hybrid TLS has grown rapidly: as of mid-2024, over 16% of human-generated requests to major content delivery infrastructure were already protected by preliminary ML-KEM hybrid key exchange, with full adoption of the finalised standard accelerating through 2025 and 2026.
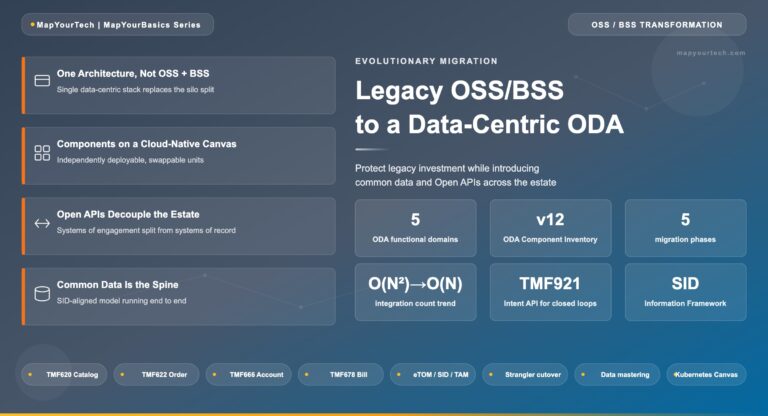
The ability to replace cryptographic algorithms without re-architecting the system is called crypto agility. Optical network operators should build crypto agility into every new hardware and software platform. This means separating key management logic from transport logic, using pluggable algorithm negotiation in management protocols, and maintaining an inventory of all cryptographic dependencies across the network. Without crypto agility, a vulnerability in a deployed algorithm requires a full hardware replacement cycle rather than a software update.
8. ION-2030 and Quantum Resilience
8.1 The ION-2030 Framework
The ITU-T Study Group 15 technical report GSTR.ION-2030, International Optical Networks towards 2030 and Beyond, defines a strategic vision for optical network evolution to support 6G mobile networks (IMT-2030), AI workloads, data centre interconnect, broadband access, home networking, and integrated sensing and communication. It was published in February 2026 and positions quantum-resilient design as one of four principal advances alongside terabit connectivity, AI-native intelligence, and energy sustainability.
The ION-2030 framework's reference to quantum resilience encompasses two elements. First, the physical layer security dimension: optical networks that will operate through the late 2030s must be designed with the assumption that QKD infrastructure may be integrated alongside classical channels, and that management plane security must be PQC-ready from inception. Second, the architecture resilience dimension: service-oriented optical architectures must support cryptographic algorithm updates without service interruption, which is a direct expression of the crypto agility principle.
8.2 ION-2030 Security Use Cases
| Network Segment | Traffic Sensitivity | Security Threat | Applicable Approach | Readiness (2026) |
|---|---|---|---|---|
| Government/Defence long-haul | Highest | HNDL, traffic analysis | QKD + AES-256 L1 encryption | Trial deployments active |
| Financial institution backbones | Very High | HNDL, record tampering | QKD or PQC + L1 encryption | PQC in design; QKD piloted |
| Carrier backbone (commercial) | Medium–High | Management plane compromise | PQC in control plane (ML-KEM, ML-DSA) | Early adoption underway |
| Data centre interconnect (DCI) | Medium–High | L1 tap, key compromise | L1 AES-256 + PQC key exchange | Deployment-ready |
| Metro / access | Medium | Management credential theft | PQC in TLS/SSH management sessions | Standards-ready; patching phase |
| Submarine cable systems | High | State-level tap, HNDL | L1 encryption; PQC for management | L1 encryption widely deployed |
8.3 AI-ION Security Interactions
ION-2030 emphasises AI-native optical networking, where AI agents make real-time decisions about routing, modulation, and restoration. This introduces new security attack surfaces. An adversary who compromises the AI decision layer — the model weights, training data, or inference API — can cause the optical network to make suboptimal or actively harmful routing decisions. PQC protects the authentication channels through which AI agents communicate; however, the integrity of AI models within optical controllers is a separate concern that ION-2030 acknowledges as an open research question in its framework.
9. Long-Term Security Planning Framework
9.1 Cryptographic Inventory and Risk Assessment
The first step in any quantum security transition is a complete inventory of cryptographic dependencies across the network. This includes TLS versions and cipher suites on management plane interfaces, SSH host key types on network elements, certificate authority chains and their algorithm choices, IPsec/IKE configurations on encrypted paths, and any proprietary encryption implementations in optical transport equipment. Without this inventory, operators cannot prioritise remediation or track migration progress.
Risk assessment should apply a secrecy horizon analysis: for each class of data in transit, estimate how long the data must remain confidential. Government communications classified for 25 years are at immediate risk from HNDL. Enterprise business data with a 5-year horizon is lower priority but should still be planned for migration. Data with a horizon shorter than the expected availability of cryptographically relevant quantum computers (commonly estimated at 2030–2035) may be deprioritised relative to longer-horizon traffic.
9.2 Migration Phases
| Phase | Timeframe | Action Items | Standards Reference |
|---|---|---|---|
| Phase 1 — Assess | 2026–2027 | Complete cryptographic inventory; identify HNDL-priority systems; evaluate L1 encryption gaps | NIST IR 8547; ETSI GR QKD 015 |
| Phase 2 — Harden Classical | 2026–2028 | Deploy AES-256 L1 encryption on all sensitive spans; disable TLS 1.2 and older; enable extended key rotation | NIST SP 800-131A Rev. 3 |
| Phase 3 — Adopt Hybrid PQC | 2027–2030 | Deploy ML-KEM hybrid (X25519MLKEM768) in management TLS; update PKI to ML-DSA certificates; test at scale | FIPS 203, FIPS 204, NIST SP 800-56C |
| Phase 4 — Full PQC Migration | 2030–2035 | Remove classical RSA/ECC from all new deployments; full ML-KEM and ML-DSA in production; prepare SLH-DSA for archive signing | NIST IR 8547 deprecation by 2035 |
| Phase 5 — QKD Integration | 2028–2035+ | Deploy QKD for high-sensitivity segments; integrate key management with PQC-protected distribution; twin-field QKD for extended reach | ITU-T Y.3800 series; ETSI GS QKD 014 |
9.3 Vendor Ecosystem Readiness
As of 2026, the major coherent optical transport vendors have announced roadmaps for L1 encryption support in their DSP ASICs. Several now offer AES-256-GCM at full line rate as a software-activated feature on deployed hardware, with key management integration as an optional add-on. Management plane PQC adoption is advancing: TLS libraries including OpenSSL 3.2+ and BoringSSL support ML-KEM and ML-DSA, enabling operating system-level updates to deploy PQC on existing network element management stacks without hardware changes. QKD integration interfaces are standardised through ETSI GS QKD 014 (key delivery API) and ITU-T Y.3800, allowing multi-vendor QKD deployments to interface with standard key management servers.
10. Comparison and Selection Guidance
| Dimension | QKD | Post-Quantum Cryptography (PQC) |
|---|---|---|
| Security Basis | Laws of quantum mechanics (information-theoretic) | Computational hardness assumptions (believed quantum-hard) |
| Threat Model | Unconditional security against any eavesdropping of quantum channel | Computationally secure; not proven unconditionally secure |
| Infrastructure | New quantum channel required (dedicated fiber or co-propagation) | Software/firmware update to existing equipment |
| Cost | High (quantum hardware, dedicated channel) | Low to moderate (software/algorithm change) |
| Distance | Limited (<150 km without trusted relays or quantum repeaters) | Unlimited (algorithm operates over any IP network) |
| Key Rate | Tens to hundreds of kbps (varies sharply with distance) | Negotiated on demand; not a constraint |
| Deployment Maturity | Commercial products available; mainly metro and regional | Standards finalised 2024; library support active in 2025–2026 |
| Standardisation | ETSI GS QKD series; ITU-T Y.3800; ISO/IEC 23837 | FIPS 203, 204, 205 (NIST); ISO/IEC work in progress |
| Regulatory Acceptance | Accepted in several national security frameworks | Mandated for US federal systems under NIST IR 8547 |
| Side-Channel Risk | Implementation attacks on QKD hardware documented | Algorithm-level attacks remain research concern (especially lattice) |
| Best Suited For | Highest-sensitivity short-to-medium haul links; government/defence | All network segments; management plane; DCI; any IP-based channel |
10.1 Decision Framework
Network operators should consider QKD when: the data has a secrecy horizon exceeding 20 years; the segment is short enough to achieve adequate key rates without excessive trusted relay nodes; budget allows for dedicated hardware; and the threat model includes nation-state actors with access to quantum computers in the near future. QKD is particularly well-justified for government or defence backbone links, inter-data-centre links carrying classified or regulated data, and financial settlement networks.
PQC should be the default choice for all other scenarios, which in practice means the vast majority of optical network deployments. It addresses the management plane threat — which QKD alone does not — and can be deployed across the entire network estate without infrastructure changes. For operators who cannot yet justify QKD investment, deploying PQC on the control plane and AES-256 L1 encryption on the data plane provides a strong near-term security posture that remains effective against HNDL attacks on the data channel while protecting the management plane against future quantum adversaries.
11. Future Directions
11.1 Quantum Repeaters
Quantum repeaters would enable QKD over continental distances without trusted relay nodes, by using entanglement swapping and quantum memory to extend quantum coherence across multiple fiber segments. Functional quantum memory with sufficient storage time and fidelity for repeater operation remains an active research area. Several groups have demonstrated quantum memory and entanglement distribution over distances of tens of kilometres; practical repeater-based networks at 1,000 km+ distances require improvements in memory lifetime, efficiency, and compatibility with telecom-band photons that are the subject of coordinated research programmes in the EU Quantum Flagship, China's QUESS expansion, and US National Quantum Initiative.
11.2 Integrated Photonic QKD
A major barrier to QKD deployment is cost and size: current systems use discrete optical components (isolators, beam splitters, single-photon detectors) assembled in rack-mounted enclosures. Integrated photonic chips that consolidate QKD transmitter or receiver functions onto silicon photonic or indium phosphide platforms promise to reduce cost by one to two orders of magnitude and to enable QKD integration into standard transceiver form factors. Research groups and startups in Europe and Asia have demonstrated chip-based QKD at lab scale; commercial chip-scale QKD integration with standard optical modules is expected within the decade covered by ION-2030.
11.3 PQC Algorithm Evolution
The NIST PQC programme is ongoing. The HQC algorithm (code-based KEM) selected in March 2025 will progress toward a draft standard in approximately 2026 with finalisation expected in 2027, providing a mathematically diverse backup to ML-KEM. NIST's additional digital signature round, with approximately 40 first-round candidates, aims to identify alternatives to ML-DSA that address specific use cases or provide diversity against lattice cryptanalysis advances. Operators building crypto-agile systems should track this programme, as algorithm updates will be software-deliverable on compliant platforms.
11.4 Post-Quantum Certificate Infrastructure
The public-key infrastructure (PKI) that underpins certificate-based authentication for optical network elements and management systems will require migration to post-quantum certificates. The first post-quantum certificates in web PKI are expected to be deployed in 2026, though not as a universal default for some time. Optical network operators managing their own private PKI hierarchies have the flexibility to migrate root and intermediate CAs to ML-DSA independently of public web PKI timelines, and should plan to do so before the NIST IR 8547 deprecation deadline of 2035.
Section Summary — Future Outlook
- Quantum repeaters are the key technology for removing trusted-relay constraints from long-haul QKD; research is active but deployment is post-2030.
- Chip-scale QKD integration will reduce hardware cost significantly, enabling broader metro deployment.
- NIST's ongoing standardisation rounds will add HQC (code-based) and additional signature alternatives to diversify algorithmic risk.
- Post-quantum PKI migration for private CAs can start now and should be completed well before the 2035 federal deprecation deadline.
12. Glossary
- AES-256-GCM
- Advanced Encryption Standard with 256-bit key in Galois/Counter Mode. Provides authenticated encryption with associated data (AEAD). The symmetric encryption standard used in Layer-1 optical encryption implementations.
- BB84
- The original QKD protocol, proposed by Bennett and Brassard in 1984, encoding key bits in the polarisation of single photons using two conjugate bases.
- Crypto Agility
- The architectural property of a system that allows cryptographic algorithms to be replaced without re-engineering the platform. Considered a baseline requirement for all new optical network equipment designs.
- CV-QKD
- Continuous Variable QKD. Encodes key information in the continuous quadrature amplitudes of light, measured using homodyne or heterodyne detection, compatible with standard coherent optical receivers.
- DV-QKD
- Discrete Variable QKD. Encodes key bits in discrete quantum states of individual photons, such as polarisation or time-bin.
- HNDL
- Harvest Now, Decrypt Later. An attack strategy in which encrypted traffic is captured and archived today for decryption when a sufficiently powerful quantum computer becomes available.
- KEM
- Key Encapsulation Mechanism. A cryptographic scheme for establishing a shared secret between two parties over a public channel, without transmitting the secret directly.
- MDI-QKD
- Measurement-Device-Independent QKD. A QKD architecture that removes all detector-side vulnerabilities by using an untrusted central relay for measurement, protecting against all detector-based side-channel attacks.
- ML-KEM
- Module-Lattice-Based Key Encapsulation Mechanism. The primary NIST PQC standard for key establishment (FIPS 203), based on the Module Learning with Errors problem.
- ML-DSA
- Module-Lattice-Based Digital Signature Algorithm. The primary NIST PQC standard for digital signatures (FIPS 204), based on lattice cryptography.
- No-Cloning Theorem
- A fundamental result of quantum mechanics stating that an arbitrary unknown quantum state cannot be copied. This theorem underpins the security of QKD against eavesdropping.
- OSNR
- Optical Signal-to-Noise Ratio. A key performance metric in optical transmission expressing the ratio of signal power to noise power in the optical bandwidth. L1 encryption is transparent to OSNR performance.
- PQC
- Post-Quantum Cryptography. Classical algorithms designed to resist attack by both classical and quantum computers, standardised by NIST through its PQC programme.
- Privacy Amplification
- A process in QKD that compresses the raw sifted key to reduce any information an eavesdropper may have obtained, producing a shorter but provably secure final key.
- QBER
- Quantum Bit Error Rate. The fraction of key bits that are received incorrectly in a QKD protocol, used to bound eavesdropper information. Eavesdropping increases QBER above the equipment noise floor.
- QKD
- Quantum Key Distribution. A family of protocols using quantum mechanical effects to generate and distribute encryption keys with information-theoretic security.
- SLH-DSA
- Stateless Hash-Based Digital Signature Algorithm. The conservative NIST PQC signature standard (FIPS 205), based on hash functions rather than lattice mathematics.
- TF-QKD
- Twin-Field QKD. A QKD protocol variant that extends the achievable distance significantly beyond standard QKD by exploiting single-photon interference at a central relay point, while retaining security against relay compromise.
References
- ITU-T GSTR.ION-2030 — International Optical Networks towards 2030 and Beyond (ION-2030), ITU-T Study Group 15.
- NIST FIPS 203 — Module-Lattice-Based Key-Encapsulation Mechanism Standard (ML-KEM), National Institute of Standards and Technology.
- NIST FIPS 204 — Module-Lattice-Based Digital Signature Standard (ML-DSA), National Institute of Standards and Technology.
- NIST FIPS 205 — Stateless Hash-Based Digital Signature Standard (SLH-DSA), National Institute of Standards and Technology.
- NIST IR 8547 — Transition to Post-Quantum Cryptography Standards, National Institute of Standards and Technology.
- ETSI GS QKD 014 — Quantum Key Distribution; Protocol and Data Format of REST-based Key Delivery API, ETSI Industry Specification Group on QKD.
- ITU-T Y.3800 — Overview on networks supporting quantum key distribution, ITU-T Study Group 13.
- V. Scarani, H. Bechmann-Pasquinucci, N.J. Cerf et al., "The security of practical quantum key distribution," Reviews of Modern Physics.
- P. W. Shor, "Polynomial-time algorithms for prime factorization and discrete logarithms on a quantum computer," SIAM Journal on Computing.
- IEEE 802.1AE — Media Access Control (MAC) Security (MACsec), IEEE Standards Association.
- Sanjay Yadav, "Optical Network Communications: An Engineer's Perspective" – Bridge the Gap Between Theory and Practice in Optical Networking.

Optical Communications & Network Automation Expert | Author of 3 Books for Optical Engineers | Founder, MapYourTech
Optical networking engineer with nearly two decades of experience across DWDM, OTN, coherent optics, submarine systems, and cloud infrastructure. Founder of MapYourTech. Read full bio →
Follow on LinkedIn